Why
The current behaviours that users have towards their online passwords and online accounts are not sufficient as it leaves them vulnerable to attacks from threat actors. Typically, passwords that users create are predictable and threat actors are able to take advantage of this in-order to successfully guess user’s passwords. Even if users purposely create passwords which they believe are unpredictable, threat actors can still use other methods to compromise organisations databases, reverse hashes and uncover the user’s password. This poses a very serious threat to cyber security as online services find it hard to distinguish malicious login attempts to legitimate ones when valid credentials are used. Within this project, this issue is tackled in-order to understand why this might be and how it can prevented with the development of a new tool which users can use to strengthen their online passwords and create strong passwords which even in the event of a data breach keeps them safe.
Comparison of modern solutions
The following table is a comparison of the 5 most popular password generators gathered from the top results of a google search and their features compared to those that have been predetermined for the password generator.
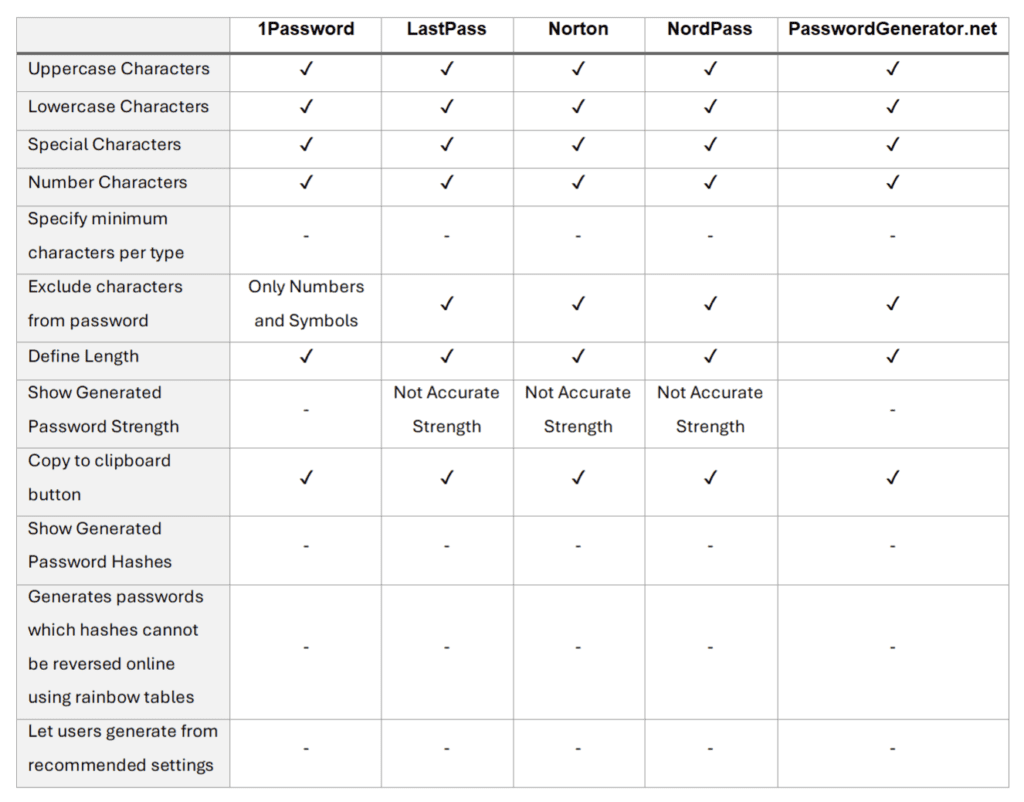
From this table, it is shown that most password generators are lacking features which protect users and encourage the use of them. These are explained below.
- No option to generate from recommended settings
As there is no option to generate from recommended settings, non-technical users are unlikely to generate strong passwords on their own as most don’t understand the difference between a weak and strong password.
- Password strength is not shown in all generators, and those that do have inaccurate strengths.
Three of the five generators had a password strength meters, however none of these had an accurate strength meter which considered both character type and password length.
LastPass and Norton generators satisfied a password with 11 characters of any type to be strong, whereas Nordpass considered if passwords were mixed with three or character more types to be strong until the password length reach 20 characters which then allowed any password with any single character type selected to be strong. This creates a problem as non-technical users will believe these passwords to be strong when they are not. This is because, for example, a password with 11 lowercase characters will produce a password with 2611 combinations whereas a password with 11 lowercase, uppercase, numerical, and special characters will produce a password with 10211 combinations. This will take significantly longer for a threat actor to brute force or create a dictionary that contains the password (Gibson Research Corporation 2022). Therefore, strong passwords should contain all four-character types and have long length which these password generators do not consider.
Three of the five generators had a password strength meters, however none of these had an accurate strength meter which considered both character type and password length. LastPass and Norton generators satisfied a password with 11 characters of any type to be strong, whereas Nordpass considered if passwords were mixed with three or character more types to be strong until the password length reach 20 characters which then allowed any password with any single character type selected to be strong. This creates a problem as non-technical users will believe these passwords to be strong when they are not. This is because, for example, a password with 11 lowercase characters will produce a password with 2611 combinations whereas a password with 11 lowercase, uppercase, numerical, and special characters will produce a password with 10211 combinations. This will take significantly longer for a threat actor to brute force or create a dictionary that contains the password (Gibson Research Corporation 2022). Therefore, strong passwords should contain all four-character types and have long length which these password generators do not consider.
- Users are unable to specify minimum characters per type.
Not allowing users to specify minimum characters per type could lead to less usage of a password generator because some services that users register to may require two or more characters within a certain character type to be present within their password. for example, the NHS password policy requires two of each character type in-order to follow best practices (NHS Digital 2022). Further, specifying the amount of character types in a password can strongly reduce the risk of brute force because the average user has primarily more lowercase and uppercase characters in their password than numbers or symbols and therefore this gives typical requirements for threat actors to create brute force dictionaries. - Generated passwords hashes are not compared to online rainbow tables to ensure they cannot be reversed or shown to user for them to lookup themselves.
If the hash values of passwords generated are able to be reversed, attacks such as SQL injection where threat actors are able to obtain password databases in hashed form could enable threat actors to get plaintext version of password and login to users accounts undetected.
Proof of concept
To justify the benefits that the proposed password generator would provide, A comparison can be made of a user generated password and one that may be generated within the password generator.
Threat actors can use tools such as Hashcat to conduct various types of hashing attacks to find plaintext of users passwords within large databases very quickly. If users are then re-using these passwords on other sites, tools such as Openbullet can quickly test username and password combinations in quick succession, even bypassing brute force protections.
Although the scenario of a user generated password has been used, the same can be true for passwords generated from online generators if in the unlikely, however possible scenario that the generated password hash has been recorded within an online rainbow table.
Without creating unique passwords and checking online rainbow tables for password hashes, there is almost no point in hashing a password within a database as it does not obscure the data for criminals if the hash can be reversed to plaintext and therefore the user is not protected. From this, there is justification for the creation of the proposed password generator that will keep users safe.
Backend Architecture
Here is the backend Architecture of the tool.

Overview of Features
Home Page
This page lets users generate passwords with hash values cannot be reversed back to plaintext values using rainbow tables.
Features
- Only generates passwords which hash value cannot be reversed using online rainbow tables.
- Generate passwords from 8 – 128 characters with a slider.
- Generate password with lowercase, uppercase, symbol and number characters.
- Specify the minimum number of characters per character type.
- Password strength meter that shows password from Strong, Medium, Bad and Very Bad.
- Recommended settings button which inputs strong password properties automatically.
- Statement to store passwords within a password manager with recommended free and paid password managers mentioned.
- Generate passwords from 8 – 128 characters with a slider.
- A password report is generated which shows information about the generated passwordThe plaintext value.
- The password strength.
- The password in hash values (SHA256, MD5, SHA, SHA224, SHA384, SHA512, BLAKE2B, BLAKE2S, SHA_224, SHA3_256, SHA_384. SHA_512).
- The individual characters within the password (lowercase, uppercase, symbols and numbers).
- The password character layout in numbered order.
- The password strength.
- A copy button to copy the generated password to clipboard.
- A description of the tool and how it keeps the user safe is displayed.
- A grid layout of features of the tool is displayed.
- An option for users to print or save to a text file the generated passwords with or without a label to make it easier for them to remember which service the password was generated for.
- An alert is presented to the user if valid options are not selected.

Check Page
This page lets users check their existing passwords cannot be reversed back to plaintext values using rainbow tables.
Features
- All that is needed to be entered by a user is the plaintext of their password, the system does the hashing in the backend itself.
- If a user’s password can be converted from a hash value to plaintext using an online rainbow table, the user is shown a notification in red text which alerts them the password is not safe to use and recommends them to replace the password with a generated password.
- If a user’s password cannot be converted from a hash value to plaintext using an online rainbow table, the user is shown a notification in green which alerts them the password is safe to use.
- A password report is generated which shows information about the user’s password
- The plaintext value.
- The password strength.
- The password in hash values (SHA256, MD5, SHA, SHA224, SHA384, SHA512, BLAKE2B, BLAKE2S, SHA_224, SHA3_256, SHA_384. SHA_512).
- The individual characters within the password (lowercase, uppercase, symbols and numbers)
- The password character layout in numbered order
- The plaintext value.
- A description of the tool is displayed.
- An alert is presented to the user if a password is not entered.

About Page
This page gives users information about this tool.
Features
- Name of creation, organisation, and motivation for creation of the tool is displayed.
- Basic features of the tool are displayed.

Contact
This page lets users contact to provide feedback, report problems or for general queries about the tool.
Features
- Button which automatically opens an email compose window with the contact email address prefilled.